Introduction to Ethical Hacking
In today’s interconnected world, where businesses and individuals rely heavily on digital infrastructure, cybersecurity has become paramount. With the rise of cyber threats, the need for skilled professionals who can protect systems and networks is more critical than ever. This is where ethical hacking comes into play.
What is ethical hacking?
Ethical hacking refers to the practice of systematically probing for vulnerabilities within a system or network infrastructure to ensure security. Unlike malicious hacking, it is sanctioned and aims to fortify cybersecurity measures.
Importance of ethical hacking in cybersecurity
With cyber threats becoming more sophisticated and prevalent, its plays a crucial role in preemptively identifying and mitigating vulnerabilities. By simulating potential attack scenarios, ethical hackers assist organizations in strengthening their defense mechanisms. demands a diverse skill set to effectively assess and secure systems against potential threats. Ethical hacking course in lahore
gives you that skills
Technical expertise
Proficiency in programming languages, networking protocols, and operating systems is indispensable for ethical hackers to comprehend complex systems thoroughly.
Problem-solving skills
Ethical hackers encounter intricate challenges while identifying vulnerabilities and devising countermeasures. Strong problem-solving abilities are instrumental in navigating through these obstacles.
Creativity and adaptability
Cyber threats are dynamic and constantly evolving. Ethical hackers must exhibit creativity and adaptability to stay ahead of adversaries and devise innovative solutions.
Understanding Cyber Realms
Types of Cyber Realms
Cyber realms encompass diverse digital environments, including networks, cloud platforms, and IoT devices. Understanding the intricacies of these realms is essential for ethical hackers to effectively assess security posture.
Importance of navigating cyber realms
Navigating cyber realms enables ethical hackers to explore and analyze potential vulnerabilities comprehensively. By understanding the intricacies of different digital environments, ethical hackers can formulate targeted strategies to bolster cybersecurity defenses.
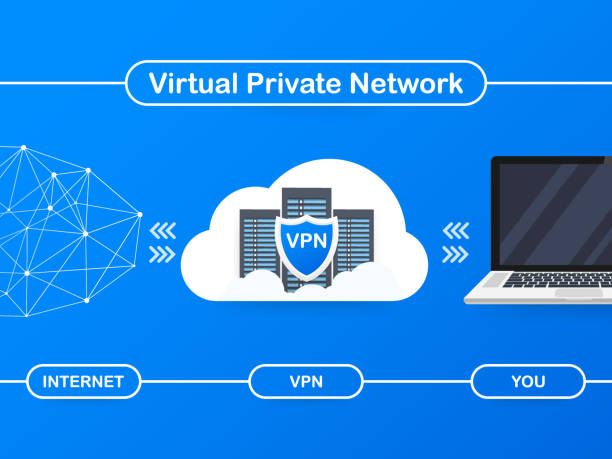
Tools and Techniques for Ethical Hacking
Ethical hackers utilize an array of tools and techniques to identify and exploit vulnerabilities within systems and networks.
Penetration testing tools
Penetration testing tools such as Metasploit, Nmap, and Wireshark enable ethical hackers to simulate real-world cyber attacks and assess the robustness of security measures.
Vulnerability assessment techniques
Vulnerability assessment techniques involve systematically scanning and analyzing systems for weaknesses and misconfigurations. Ethical hackers employ techniques like port scanning, vulnerability scanning, and password cracking to identify potential entry points for attackers.
Ethical Hacking Methodology
its follows a structured methodology to ensure thorough assessment and mitigation of vulnerabilities.
Reconnaissance
During the reconnaissance phase, ethical hackers gather information about the target system or network, including IP addresses, domain names, and network topology.
Scanning
Scanning involves actively probing the target system or network to identify open ports, services, and potential vulnerabilities.
Gaining access
Ethical hackers exploit identified vulnerabilities to gain unauthorized access to the target system or network, simulating real-world cyber attacks.
Maintaining access
Once access is gained, ethical hackers strive to maintain persistence within the target environment to assess the extent of potential damage and identify additional vulnerabilities.
Covering tracks
Ethical hackers cover their tracks by removing evidence of their presence within the target system or network to maintain confidentiality and integrity.
Legal and Ethical Considerations
Ethical hacking must adhere to legal and ethical guidelines to ensure responsible conduct and avoid legal repercussions.
Laws and regulations
Ethical hackers must familiarize themselves with relevant laws and regulations governing cybersecurity practices, such as the Computer Fraud and Abuse Act (CFAA) in the United States.
Code of conduct for ethical hackers
Professional organizations like the EC-Council and CompTIA provide ethical hacking certifications and guidelines to promote ethical conduct and professionalism within the cybersecurity community.
Challenges and Risks
Ethical hacking presents various challenges and risks that must be addressed to ensure effective security assessment and mitigation.
Evolving threats
Cyber threats continue to evolve, necessitating continuous learning and adaptation among ethical hackers to stay abreast of emerging vulnerabilities and attack vectors.
Mitigating risks
Ethical hackers must employ robust risk management strategies to minimize the potential impact of security breaches and safeguard sensitive information.
Benefits of Ethical Hacking
Ethical hacking yields numerous benefits for organizations seeking to bolster their cybersecurity posture and protect against cyber threats.
Strengthening cybersecurity
By identifying and remedying vulnerabilities, ethical hacking helps organizations fortify their defenses and mitigate the risk of cyber attacks.
Identifying vulnerabilities before malicious actors
Ethical hacking enables organizations to proactively identify and address vulnerabilities before they can be exploited by malicious actors, thereby reducing the likelihood of data breaches and security incidents.
Ethical Hacking Certifications
Ethical hacking certifications validate the skills and expertise of professionals in the field of cybersecurity.
Certified Ethical Hacker (CEH)
CEH certification equips individuals with the knowledge and skills required to assess and mitigate security risks through ethical hacking techniques.
Offensive Security Certified Professional (OSCP)
OSCP certification demonstrates proficiency in penetration testing and offensive security techniques, validating the ability to identify and exploit vulnerabilities within systems and networks.
Career Opportunities in Ethical Hacking
offers a plethora of career opportunities for individuals passionate about cybersecurity and technology.
Penetration tester
Penetration testers assess the security posture of organizations by simulating cyber attacks and identifying vulnerabilities that could be exploited by malicious actors.
Security analyst
Security analysts analyze security incidents and implement measures to protect against cyber threats, utilizing techniques to fortify organizational defenses.
Conclusion
Ethical hacking serves as a proactive approach to cybersecurity, enabling organizations to identify dark web safety and mitigate vulnerabilities before they can be exploited by malicious actors. By understanding the essentials and navigating cyber realms effectively, individuals can contribute to the ongoing efforts to safeguard digital infrastructure and protect sensitive information.
FAQs (Frequently Asked Questions)
- What is the difference between ethical hacking and malicious hacking? it is conducted with permission and aims to improve cybersecurity, while malicious hacking involves unauthorized access for malicious purposes.
- How can I become an ethical hacker? To become a hacker, one should acquire relevant certifications, develop technical skills, and adhere to ethical guidelines and regulations.
- What are the legal implications? must ensure compliance with laws and regulations governing cybersecurity practices to avoid legal repercussions.
- What role does ethical hacking play in cybersecurity? helps organizations identify and mitigate vulnerabilities, thereby strengthening their cybersecurity defenses and reducing the risk of cyber attacks.
- Are certifications necessary for a career in cybersecurity? While certifications are not mandatory, they demonstrate proficiency and expertise in hacking techniques, enhancing career prospects in cybersecurity.